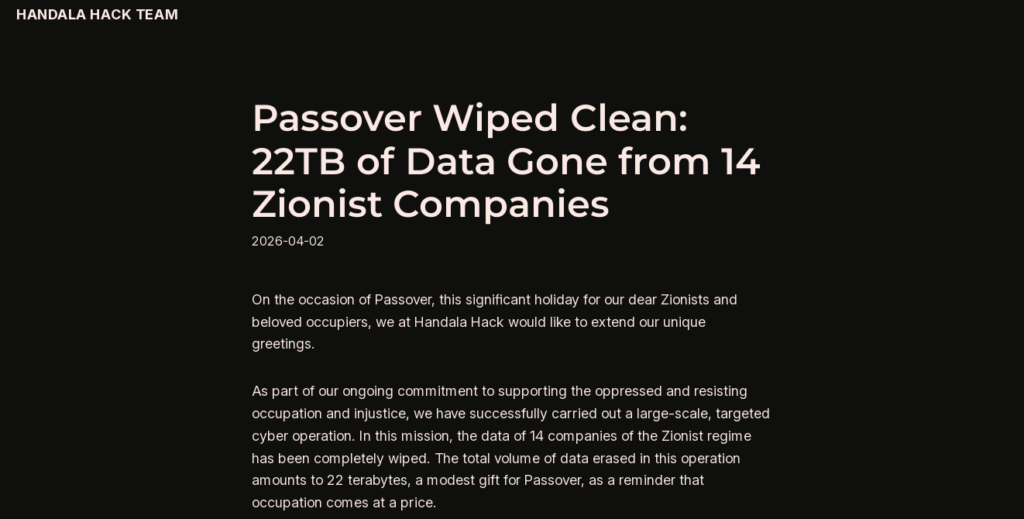
On March 11, 2026, the medical technology giant Stryker Corporation experienced a large-scale cyber incident representing an escalation in Iranian cyber operations. The Iran-linked group Handala claimed it had wiped over 200,000 systems across 79 countries. While these figures are likely inflated as part of information operations, subsequent reporting suggests approximately 80,000 affected devices. The operational impact was significant: employees across the globe were unable to access their corporate devices, with login screens replaced by Handala branding.
Handala is widely assessed to operate as more than a “hacktivist” collective; it functions as a persona leveraged by Iran’s Ministry of Intelligence and Security (MOIS) to conduct destructive cyber operations. In this incident, Handala leveraged privileged administrative access within Microsoft Intune to control and wipe devices at scale. This activity reflects a shift from data exposure toward enterprise-scale disruption, consistent with previously observed Iranian cyber operations.
The Laboratory of Conflict: Why the Warning Signs Were Ignored
The Stryker incident reflects a potential escalation in Iranian cyber activity. Handala’s prior activity, particularly in Israel, is best understood as a multi-year operational environment in which capabilities and tradecraft were refined.
- The Proving Ground: Since 2023, Handala has targeted Israeli sectors including healthcare, technology, government, energy, and defense, likely refined tooling, access methods, and disruptive capabilities, including wiper functionality.
- Operational Synergy: Observed activity suggests a “hand-off” model, where cyber espionage groups like APT43 (OilRig) secure initial access before activity is carried out by separate clusters or personas, including Handala, for disruptive or destructive effects.
- Proxy Integration: Handala operates alongside hacktivist personas and state-aligned clusters, contributing to a resilient operational ecosystem.
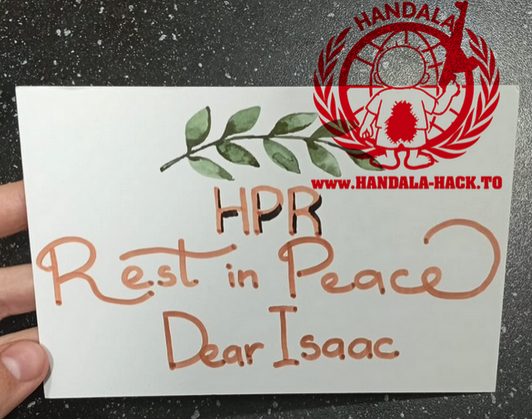
- Beyond the Digital Border: As observed in the 2025 “Rest in Peace” operation referenced below, Handala’s activity has extended to psychological intimidation and individual targeting, indicating an expansion beyond purely digital operations.

From “Hacktivism” to State-Linked Disruption in Israel
Handala’s activity has evolved beyond DDoS and data leaks to include disruption and psychological targeting.
The RedWanted Platform
The launch of the “RedWanted” platform in November 2025 represents a notable development. The platform appears to function as a publicly accessible, searchable, bounty-style site that extends targeting beyond digital systems to individuals, introducing elements of real-world intimidation influence.
- Targeting the “Brain Power”: Operations extend to individuals linked to sensitive organizations including the Weizmann Institute of Science, Elbit Systems, and Soreq Nuclear Research Center, as well as associated scientists and researchers.
- The “Bounty” Model: The site appears to operate as a targeting mechanism, displaying images of individuals with a “crosshair” overlay, and encouraging users to gather information, including references to locating nearby traffic cameras or conducting physical observation.
- Psychological Pressure: By leaking personal information and reportedly placing “Rest in Peace” flowers in a target’s vehicle, the activity suggests potential real-world intimidation tactics, extending beyond purely digital operations.
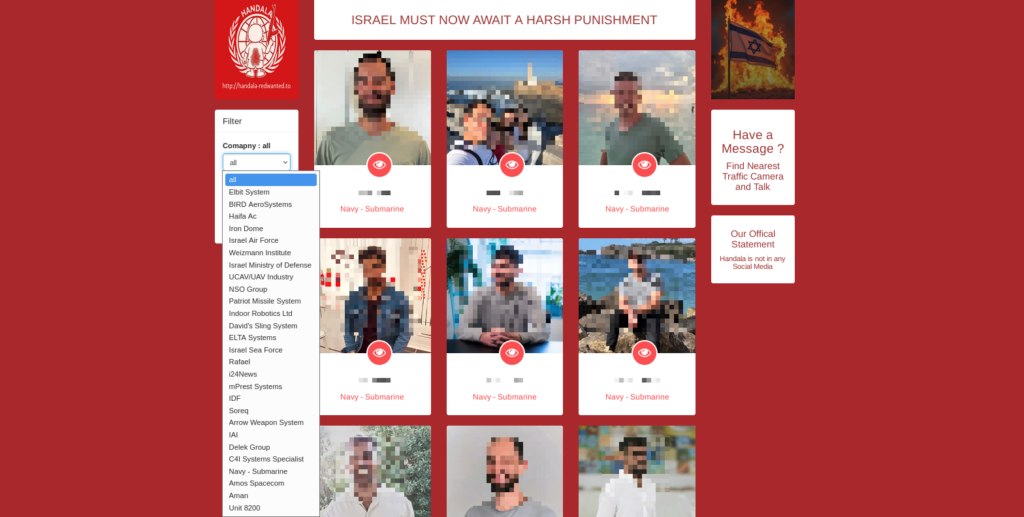
Operational Influence: This activity may provide context for the Stryker incident, demonstrating how the combination of data exposure and public intimidation can be used to pressure individuals and organizations in sensitive sectors.
Beyond Hacktivism: The Manticore Operational Ecosystem
To understand Handala, it is useful to examine the broader “Manticore” ecosystem, an analytical framework describing clusters associated with Iranian cyber operations that perform distinct but complementary roles. In this model, different units focus on functions such as espionage, influence, and disruptive activity. The term “Manticore,” drawn from Persian mythology, is used here as a conceptual shorthand rather than a formal designation.
Disruptive Operations: Void Manticore (Handala)
Tracked by researchers as Void Manticore (Banished Kitten, Storm-0842, Dune, Bad Karma, No Justice, and Red Sandstorm), this cluster is widely assessed to be aligned with Iran’s Ministry of Intelligence and Security (MOIS).
- Specialty: Disruptive and destructive operations, including data exposure and wiper activity associated with later-stage intrusion phases.
- Tooling: Their most well-documented capability includes the “Bibi Wiper,” malware designed to overwrite files and render systems inoperable.
Espionage Operations: Scarred Manticore
While Handala is more visible, Scarred Manticore is associated with lower-profile, access-oriented activity. This cluster is linked to activity commonly attributed to groups such as APT43 (OilRig).
- Specialty: Long-term espionage and initial access operations.
- Operational Model: These actors may maintain persistent access within target environments, mapping infrastructure and harvesting credentials before activity is conducted by separate clusters. This pattern is consistent with a “hand-off” model observed in Iranian cyber operations.
Influence Operations: Maimed Manticore
Maimed Manticore is associated with influence and information operations, functioning as part of a broader ecosystem of state-aligned narrative and propaganda activity.
- Specialty: Creation and dissemination of content designed to influence perception, often leveraging social media platforms and coordinated inauthentic behavior.
- Tactics: Activities may include the use of fabricated personas, amplification networks, and websites designed to mimic legitimate sources, contributing to the spread of aligned narratives.
IRGC-CEC Operations and Corporate Fronts
Unlike the MOIS, which leverages personas such as Handala for disruptive cyber operations, including wipers and data exposure, the IRGC-CEC is associated with activity aligned to Iran’s military apparatus. Its operations prioritize disruptive cyber activity and influence operations, often conducted through front personas such as CyberAv3ngers, targeting high value Israeli and Western entities.
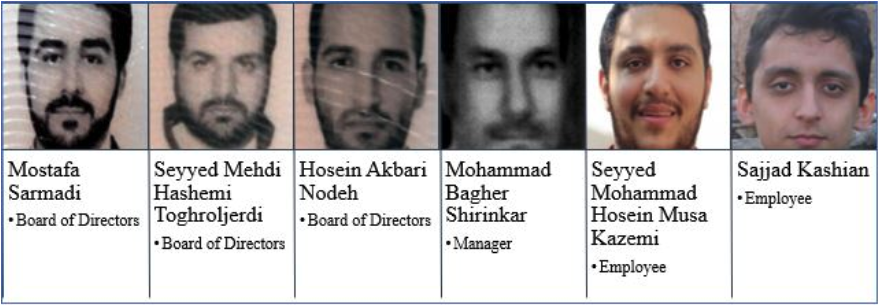
Emennet Pasargad (a.k.a. Shahid Shushtari)
Tracked by the intelligence community as Cotton Sandstorm, Emennet Pasargad is a sanctioned Iranian entity associated with cyber and influence operations. The organization has demonstrated a pattern of rebranding and alias usage, including names such as Net Peygard Samavat, Eleyanet Gostar, and Imannet Pasargad, likely to evade sanctions and attribution.
- The Facade: The entity operates as a nominally legitimate company within Iran, providing infrastructure, funding, and operational support for state-aligned cyber actors.
- Associated Personas: Emennet Pasargad has been linked to multiple online personas and clusters, including Holy Souls, Neptunium, and CyberAv3ngers.
- Holy Souls: Linked to data exposure activity, including the 2023 Charlie Hebdo-related incident.
- CyberAv3ngers: Associated with targeting critical infrastructure, including industrial control systems such as Unitronics PLCs.
| Sanctions and Operational Activity Emennet Pasargad is sanctioned by the U.S. government and linked to Iranian state-aligned cyber and influence operations, including U.S. election interference, disinformation campaigns, and cyber activity targeting media and voting-related infrastructure. More recent reporting indicates the group has incorporated generative AI into influence operations, including campaigns such as “For Humanity,” which involved compromising a U.S.-based IPTV service to distribute propaganda related to the Israel-Hamas conflict. |
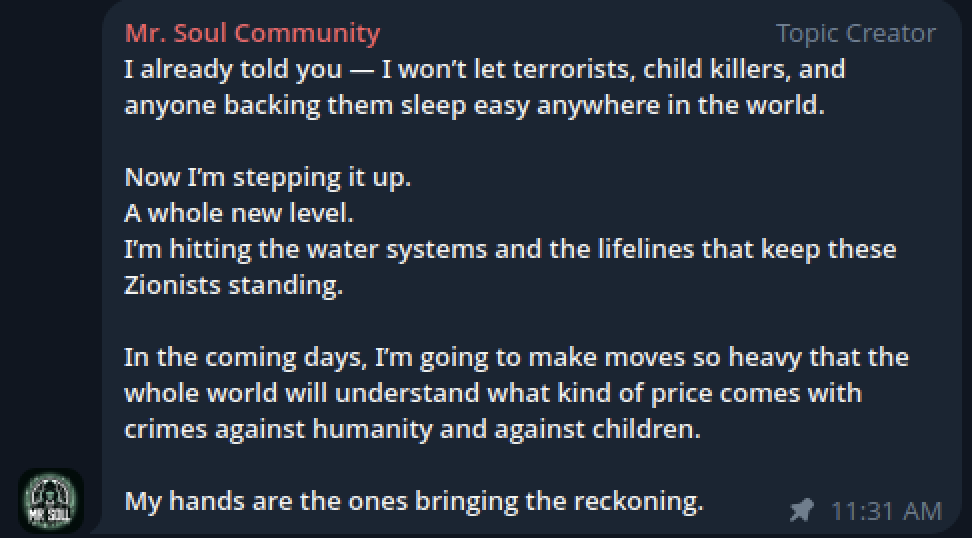
The ICS Saboteurs: CyberAv3ngers
Since 2023, the IRGC-CEC has used the “CyberAv3ngers” persona to target Western and Middle Eastern critical infrastructure. The group consistently targets technologies associated with Israeli manufactures, aligning with broader Iranian cyber activity.
- Targeting Water Infrastructure: Beyond the 2023 attack on Municipal Water Authority of Aliquippa, the group has expanded to desalination and filtration systems. In March 2026, CyberAv3ngers was reportedly linked to activity affecting the Ras Abu Jarjur desalination plant in Bahrain. By exploiting internet-exposed Unitronics Vision Series (e.g. TCP port 20256), operators may manipulate industrial processes, including reverse osmosis and chemical treatment. This highlights the potential for cyber operations to impact physical infrastructure.
- Specialized Tooling: IOCONTROL: This group uses IOCCONTROL, a Linux-based wiper targeting industrial control systems (ICS) across sectors such as food processing, rail, and municipal water. By disrupting operator visibility and control, it can create conditions where physical processes may be affected without immediate detection.
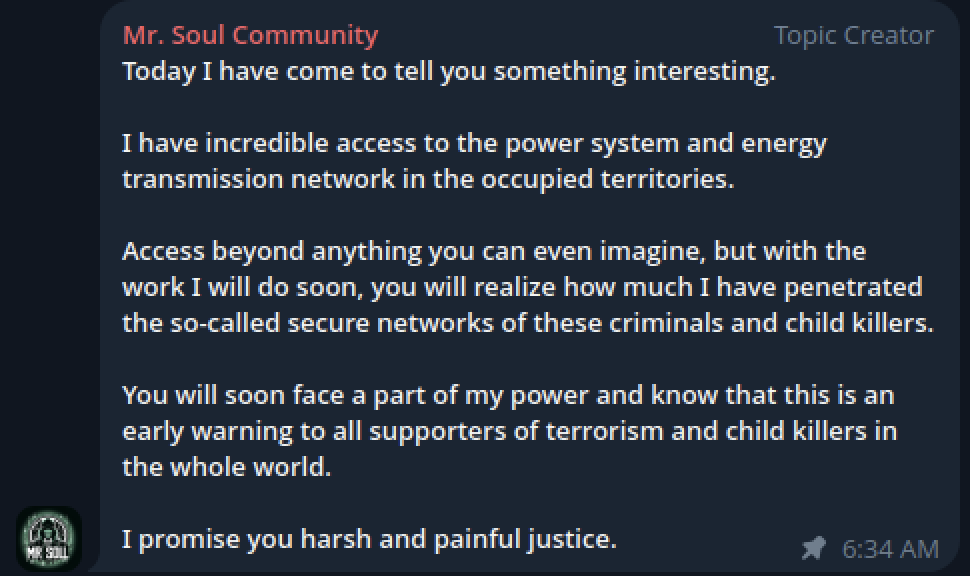
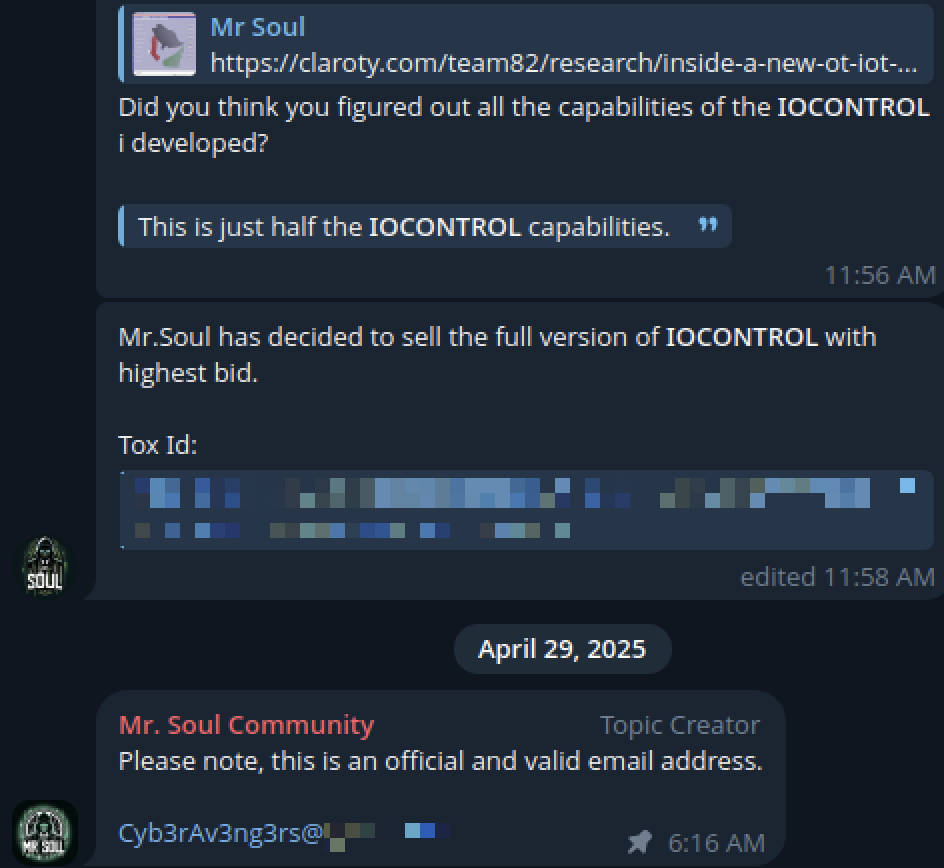
The Bridging Point: Mr. Soul
Mr. Soul (a.k.a Mr. Sol) is an Iranian-linked developer associated with tooling and online activity, potentially linking multiple operational clusters.
- Operational Shift: By late 2025, Mr. Soul shifted from low-profile activity to promoting Handala-linked operations via Telegram, aligning more closely with Handala than other associated clusters.
- Cross-Cluster Alignment: This shift may indicate increasing alignment between IRGC and MOIS linked activity, suggesting a more coordinated operational posture.
- Sanctioned Leadership: The U.S. sanctioned Mahdi Lashgariam as a senior IRGC-CEC figure. His relationship to the Mr. Soul persona remains unclear, but the overlap highlights links between leadership and observed activity.
- Tooling Attribution: Mr. Soul is associated with IOCONTROL, which has been linked to disruptive ICS-focused operations.
The Operational Hand-Off Model
The interaction between clusters such as Scarred Manticore and Handala is best understood as a structured, multi-phase operational model, rather than a loosely coordinated effort. Observed activity suggests a repeatable pattern involving access, persistence and subsequent disruptive action, consistent with the March 11 Stryker Corporation incident.
Phase 1: Access and Persistence (“Low and Slow” Infiltration)
Initial access activity is typically associated with espionage-oriented clusters such as Scarred Manticore (linked to APT34), whose objective is environmental visibility and credential access rather than immediate disruption.
- Objective: Establish persistent access, map network architecture, and obtain high-privilege credentials (e.g. domain or cloud administrative access).
- Tradecraft: Activity has included use of frameworks such as LIONTAIL and techniques such as DNS tunneling, enabling long-term access while blending with legitimate traffic and evading detection.
- Data Exposure Risk: During this phase, actors may collect sensitive data, including internal communications and credentials, which can later be used to amplify disruption or public exposure.
Phase 2: Disruption and Impact (“Handala” Activity)
Once access and credentials are established, activity may transition to clusters such as Handala (Void Manticore), which conduct disruptive or destructive operations.
- Operational Shift: Handala leverages previously obtained access to escalate privileges and execute disruptive actions within the environment.
- Destructive Activity: This phase may involve deployment of wiper malware or other destructive techniques, impacting data integrity and system availability.
Abuse of Native Tools: In more advanced cases, actors leverage legitimate enterprise management platforms, such as Microsoft Intune, to issue authorized commands (e.g., device resets) at scale, effectively using the organization’s own infrastructure to carry out disruption.
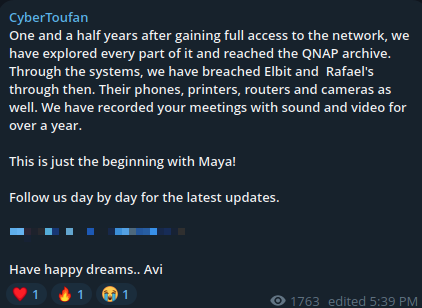
Pattern Replication: CyberToufan
Another group that mirrors aspects of Handala’s activity is CyberToufan (Cyber Toufan Al-Aqsa). While operating as a distinct persona, CyberToufan demonstrates similar operational patterns and messaging, suggesting reuse of tradecraft across clusters.
- Replicated Model: Both personas exhibit a similar operational pattern, in which access-oriented activity, often associated with groups such as APT34, is followed by more visible disruptive activity. This two-phase approach aligns with previously observed Iranian cyber operations.
- Shared Infrastructure Indicators: Overlap between the groups is visible in elements such as Telegram bots, leak site formatting, and communication patterns, suggesting shared tooling or infrastructure components, rather than purely independent activity.
- Psychological Targeting: Both personas incorporate human-centric targeting, including exposure of internal communications and sensitive materials. While Handala has utilized platforms such as RedWanted, CyberToufan has conducted “boardroom-style” leaks, releasing recordings and internal content to demonstrate access within targeted organizations.

Defensive Posture: Disrupting the Operational Model
To mitigate activity associated with Handala and related clusters, organizations should consider the following controls:
- Restrict “Wipe” Permissions: Implement multi-admin approval (MAA) in Microsoft Intune for high impact actions. No single account should be able to initiate large-scale device resets.
- Enforce Phishing-Resistant MFA: Require FIDO2 hardware security keys (e.g. YubiKey) for privileged accounts to mitigate adversary-in-the-middle (AiTM) attacks.
- Secure “Break-Glass” Accounts: Maintain isolated emergency accounts, secured with hardware-based authentication and high-priority alerting for any login attempts.
- Audit External Exposure: Use tools such as Shodan and Censys to identify exposed services, including RDP, VPNs, and public repositories.
Closing Part 1: The Illusion
The March 11, 2026, incident affecting Stryker Corporation was not an isolated event, but the culmination of a multi-year evolution in Iranian cyber operations. Activity observed across sectors and regions reflects a consistent operational model combining access, disruption, and narrative amplification.
Rather than independent “hacktivist” activity, this pattern suggests a structured ecosystem in which personas such as Handala serve as the public-facing layer of broader state-aligned capabilities. The Stryker incident demonstrates how this model can scale beyond regional targets into enterprise environments.
Part 2: The Hydra’s Reach
Part 2 moves beyond the Handala persona to examine the individuals and groups operating behind and alongside these identities, shifting from the operational model to the actors who sustain and amplify it. Building on investigative reporting, including work by Nariman Gharib and the Iran International team, it highlights how elements of this ecosystem have begun to lose anonymity, while activity across multiple groups since 2023 suggests increasing convergence in tactics, infrastructure, and messaging. The following analysis focuses on key actors and how they extend the reach and impact of this broader operational framework.
Structure and Defenses of Underground Forums
CONTENTS

We examine underground forums where stolen data is traded and network access is sold: their access model, commerce mechanisms, anti-scraping defenses, and what it takes to collect data from them at scale.
These underground forums attract initial access brokers, ransomware affiliates, fraud operators, and data brokers. Most run on popular forum software (such as MyBB, XenForo, Invision Community), and that shared foundation means a single extraction approach can cover many targets with minimal adaptation. What makes them different is the architecture layered on top.
Surface Level
At first glance, the common structure of an underground forum looks familiar: categorized sections, thread listings, user profiles. The sections are commonly gated by account tiers: public (unauthenticated), authenticated, premium (paid), and manually vetted.
Some underground forums allow guest browsing with no account required, so the public layer is visible to anyone with a Tor browser. But even within visible threads, individual posts may hide their payload behind a credit cost, a reply requirement, or an access level. Sellers and brokers advertise in the open and mostly transact behind the paywall. What any given tier exposes varies by site: some have substantial public content, while others gate nearly everything.
Marketplace and Actors
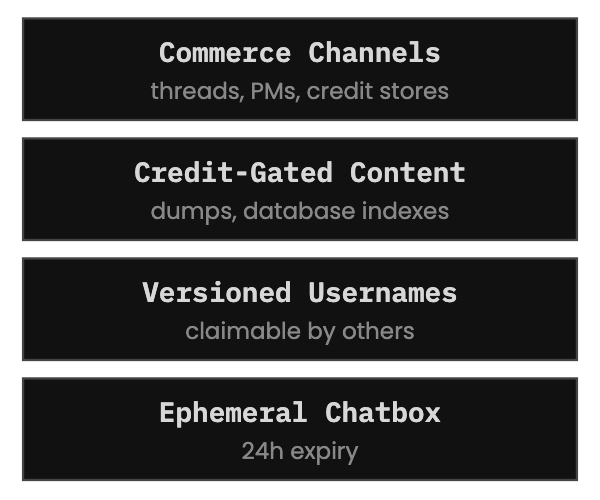
Most underground forums have no formal marketplace (no cart, no order system). Actors sell through threads and private messages, posting samples (record counts, a handful of rows, redacted excerpts) as proof, and gating the full dump behind credits or private negotiation.
Capturing these is time-sensitive. Listings can be edited or deleted without notice. Some platforms go further with a database index where users can browse available dumps and spend credits to unlock them directly.
Usernames can be versioned, making tracking difficult. A username change we missed means a gap in the attribution chain. Some underground forums allow abandoned handles to be claimed by other accounts, which compounds the problem. The same username may represent different actors a month apart.
Beyond threads and posts, which are mostly static, these platforms also have an ephemeral layer: chatbox messages that commonly expire within 24 hours. This is one of the narrowest capture windows in the system.
Defense Mechanisms
The underlying engine is common forum software. What sits on top of it is hardened.
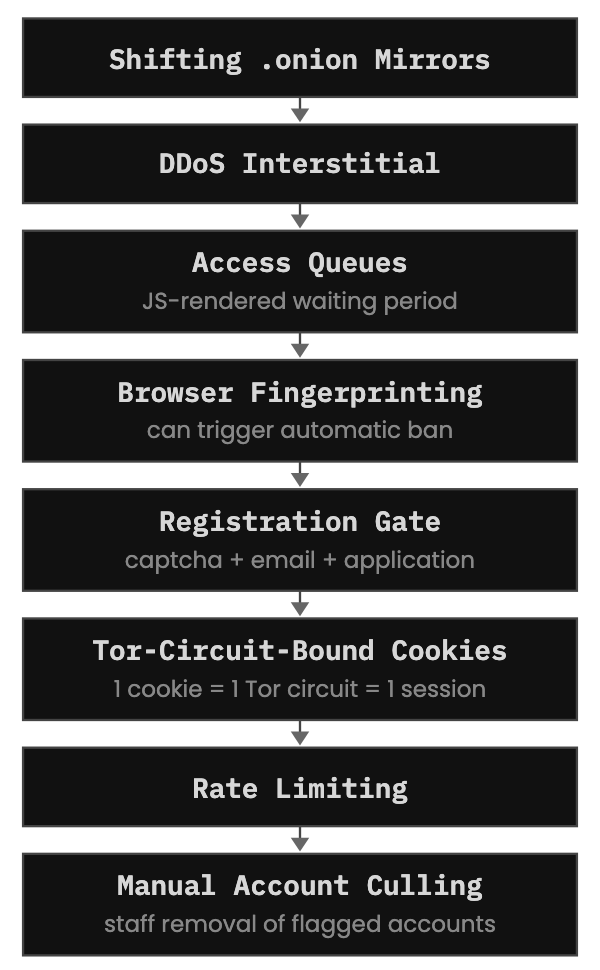
Although some underground forums operate on the clear net, many run as Tor hidden services where domains shift across multiple .onion mirrors that rotate, go down, or are chosen by user polls. These need to be tracked and treated as a single source. New mirrors have been observed masquerading as seized or defunct ones. Data sourced from mirrors must be treated as mutable, so it can be corrected during analysis.
Beyond technical defences, access itself is gated. Some underground forums require vouching: an existing member stakes their reputation on the newcomer’s behavior. If the newcomer burns trust, the voucher takes the hit. Others gate sections behind minimum post counts, forcing new accounts to contribute before reaching anything valuable. Premium tiers are paid in cryptocurrency. Staff also manually cull accounts that exhibit suspicious patterns (automated browsing behavior, dormant registrations, or anomalous request volumes).
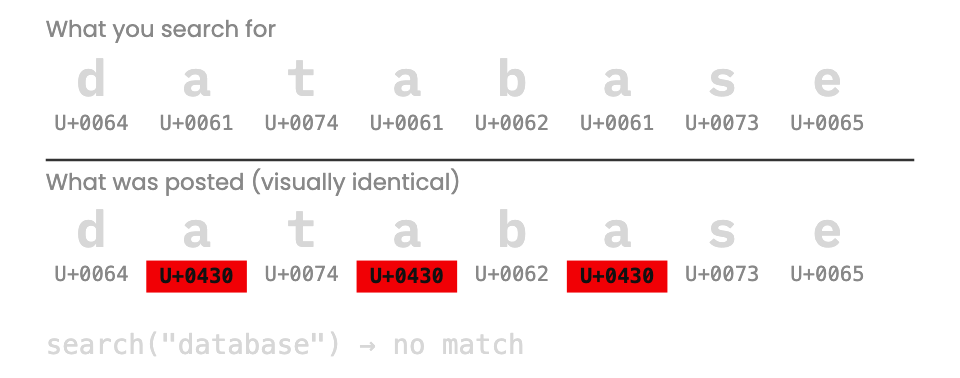
Some users implement their own countermeasures. One tool we observed uses homoglyph obfuscation (replacing Latin characters with visually identical Cyrillic ones). To a human reader the text looks normal. To a scraper or keyword search, it’s unusable. A technique borrowed from phishing, repurposed as a direct counter to the knowledge that they are being scraped.
What Collection Requires
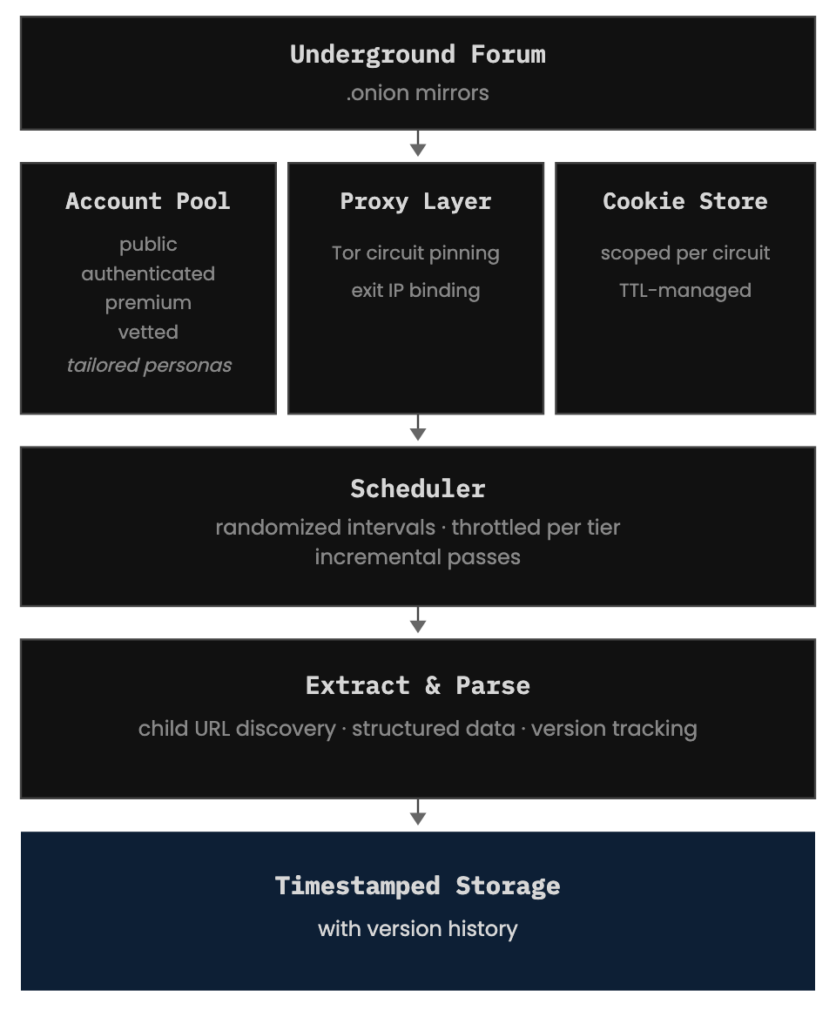
Collecting at scale requires:
- Account management across access tiers, each with a tailored persona (specific timezone, browsing pattern, activity profile).
- Session handling and cookie persistence, scoped per account and Tor circuit. Each session cookie must stay bound to the Tor circuit and exit IP it was issued on. Mixing cookies across Tor circuits or accounts triggers recaptcha events.
- Proxy orchestration: Tor circuit pinning to maintain session continuity. Request patterns must appear organic (varying intervals, non-sequential page access) because underground forum operators can and do inspect their logs.
- Scheduling and throttling: aggressive on public content, conservative on premium accounts. Some underground forums have a large volume of public content worth collecting.
- Text normalization: homoglyph detection, leetspeak decoding, multilingual content.
- Timestamped storage for everything we capture.
Every record is versioned. Mutations between collection passes are tracked as events, not overwritten. The history of changes is itself data.
Conclusion
Underground forum operators know they’re being scraped, and they adapt accordingly. Defenses gain another layer. New interstitials appear. Tor-circuit binding tightens. More log-checking and account culling.
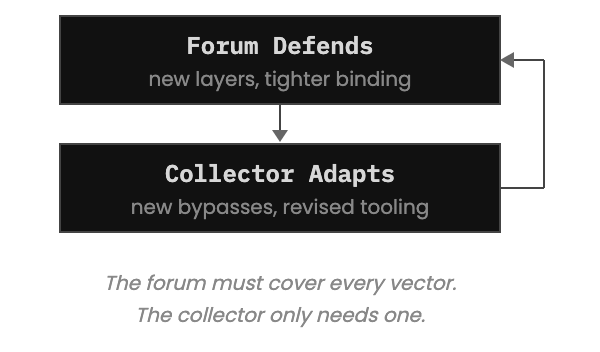
The asymmetry between attacker and defender (where one side needs a single gap while the other must cover every surface) is usually cited in favor of threat actors targeting orgs. In the collection domain, that asymmetry inverts. The underground forum must defend every vector. The collector only needs one that works.
But gaining access is only the first problem. Infrastructure shifts, countermeasures evolve, content expires: maintaining collection through all of it is continuous work. One mistake can burn an account that took months of persona-building and paid access to establish.
The analysis that follows (tracing aliases, detecting deletions) depends on what was captured and when. Every gap weakens the attribution chain. The infrastructure to close those gaps must be tended for as long as the forums run.

On February 24, 2026, the U.S. invoked the first-ever sanctions under the Protecting American Intellectual Property Act (PAIPA). The primary target: Russian national Sergey Zelenyuk and his exploit brokerage, Operation Zero (legally known as Matrix LLC).
Why this matters
This move marks a major pivot in U.S. strategy. By invoking PAIPA, the government is officially classifying the illicit trade of zero-day vulnerabilities as a direct threat to national security.
For the CTI community, this is a rare, high-visibility strike against the “gray market” commercial brokers who monetize government-grade flaws for foreign intelligence and criminal groups.
| PAIPA (Public Law 117-336) authorizes the President to impose aggressive sanctions on any foreign entity that steals, benefits from, or supports the theft of U.S. trade secrets. Under the International Emergency Economic Powers Act, the government can freeze assets, block all U.S. transactions, and blacklist entities from the Commerce Department’s Entity List. The February 2026 sanctions against Operation Zero mark the first operational use of these powers, signaling a new era of disruption against “exploit-as-a-service” markets and critical technology theft. |
The Operation Zero Playbook: Mercenary Exploits
Since 2021, Operation Zero has disrupted the traditional vulnerability market by operating as a pure mercenary broker. Unlike “white-hat” programs that help vendors patch bugs, this firm stockpiles flaws to weaponize them for the highest bidder—specifically courting the Russian government.
The Insider Threat: The Peter Williams Case
The firm’s rise was fueled by a massive security breach. Between 2022 and 2025, Australian national Peter Williams—a former manager at U.S. defense contractor L3Harris (Trenchant)—betrayed his position by stealing eight proprietary zero-day components.
- The Deal: Williams sold these “government-only” tools to Operation Zero for $1.3 million in cryptocurrency.
- The Fallout: Williams pleaded guilty to theft of trade secrets in October 2025. On February 24, 2026, he was sentenced to over seven years in federal prison.
Escalating the Arms Race
Operation Zero isn’t just buying exploits; they are outbidding the entire industry. In late 2023, the firm sent shockwaves through the CTI community by offering staggering bounties:
- Payouts: Up to $20 million for full-chain Android and iOS exploits.
- The Catch: The firm explicitly states that the end user must be a “non-NATO country.” By setting prices significantly higher than competitors like Zerodium or Crowdfense, Operation Zero has effectively cornered the “gray market” for state-level offensive cyber tools.
The Network: Operation Zero & Its Affiliates
The February 2026 sanctions target a sophisticated, global web of shell companies and cyber-mercenaries. By placing these names on the OFAC SDN List, the U.S. has effectively frozen their global assets and barred them from the international financial system.
Core Entities & Leadership
- Operation Zero (Matrix LLC): The St. Petersburg-based “mothership” of the network. Founded in 2021 by Sergey Zelenyuk, it functions as a full-service exploit broker, supplying high-end surveillance and espionage tools to non-NATO intelligence services.
- Sergey Sergeyevich Zelenyuk: The architect and sole owner. Zelenyuk is the primary target of this action, identified as the kingpin of this mercenary network.
- Marina Vasanovich: Zelenyuk’s personal assistant and operational lead, responsible for client logistics and coordinating the sale of stolen trade secrets.
The Infrastructure of Evasion
- Special Technology Services (STS) [UAE]: A front company Zelenyuk established in late 2024 to bypass Russian bank sanctions and facilitate “gray market” sales in Asia and the Middle East.
- Advance Security Solutions [Dubai/Uzbekistan]: A parallel brokerage founded by Azizjon Mamashoyev. It acts as a secondary sourcing arm, masking the origin of exploits before they reach Operation Zero.
The Criminal Connection
- Oleg “GABR” Kucherov: A high-level Russian national and suspected member of the notorious TrickBot cybercrime gang. Kucherov provided the technical and financial backbone that allowed Operation Zero to bridge the gap between criminal ransomware and state espionage.

Strategic Recommendations for CTI
- Financial Surveillance: Monitor OFAC-listed crypto wallets and track new addresses linked to the $20M mobile-exploit bounties.
- Exploit Fingerprinting: Integrate the eight stolen components and advertised iOS/Android chains into internal IOC repositories.
- Priority Patching: Treat Operation Zero’s “Target List” as a high-priority roadmap for vulnerability management.
- Collective Defense: Share attribution data with ISACs to flag downstream abuse of these high-value exploits.
The Final Verdict
The PAIPA sanctions against Operation Zero mark a watershed moment—a powerful new lever the U.S. is now wielding against “exploit-as-a-service” markets. This isn’t just a legal update; it’s a shift in the digital balance of power.
The invocation of PAIPA means these individuals are no longer just “brokers” in the eyes of the law—they are now official threats to national security.
“If you steal U.S. trade secrets, we will hold you accountable.”
— Treasury Secretary Scott Bessent, February 24, 2026